The Solution
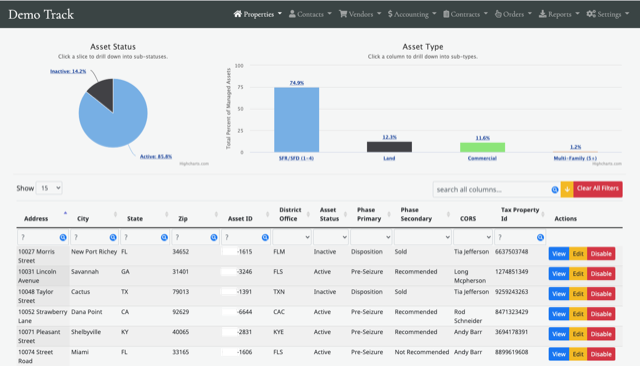
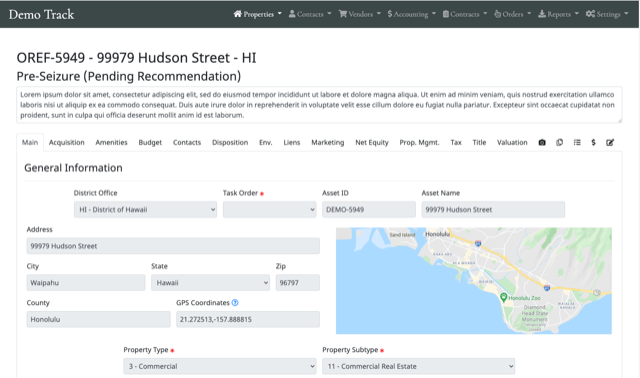
Our initial solution was a straight-forward web application, built on the LEMP stack and hosted in Amazon AWS. It allowed multiple users, with varying permission levels, to access and update all the data (and more) stored within the original spreadsheet. In addition to proper reporting, it also allowed for CSV imports of raw data.
The solution was so well received, we were contracted to expand and improve upon it. Opting for a more modular approach that would allow for future development, we used the Laravel framework to build version 2.0. This gives us flexibility and allows for the rapid development and deployment of new features. After passing government penetration tests and security audits, the system is now is use by two federal agencies, with over 250 active users (and support for thousands).
Our system has a strong emphasis on permission-based security, with over 225 unique permissions assignable to various roles throughout the system. In addition, nearly every action taken on the site is logged for auditing purposes.
In addition to regular data management, we built a public facing marketing site to aid our client’s sales teams. With security as our top focus, we installed the marketing site on an isolated server, with data being pushed to it via a one-direction, read-only SSH tunnel. If the public server were ever compromised, the internal servers will be inaccessible to attackers.